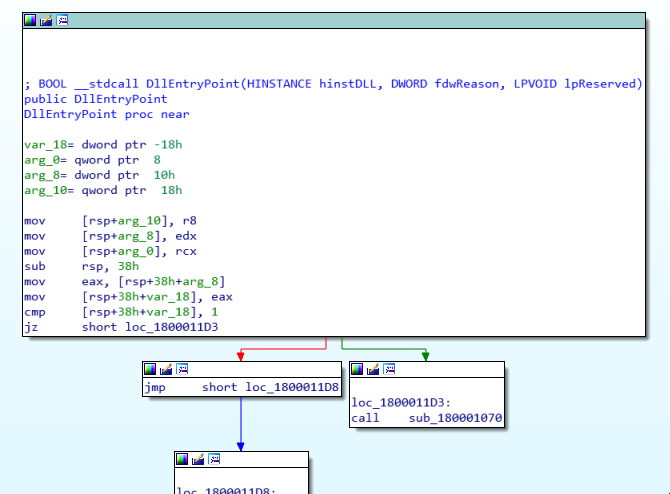
Abusing Exceptions for Code Execution, Part 2
Por um escritor misterioso
Last updated 24 abril 2025
In this article, we'll explore how the concepts behind Exception Oriented Programming can be abused when exploiting stack overflow vulnerabilities on Windows.

What is a Buffer Overflow Attack Types and Prevention Methods

exception processing message 0xc0000005 - unexpected parameters

Abusing Exceptions for Code Execution, Part 2

Why Instagram Threads is a hotbed of risks for businesses
Sample Terms of Use Template and Guide - Termly

Defining 'Abusive Conduct' Under California Law: A

Why the C Programming Language Still Runs the World
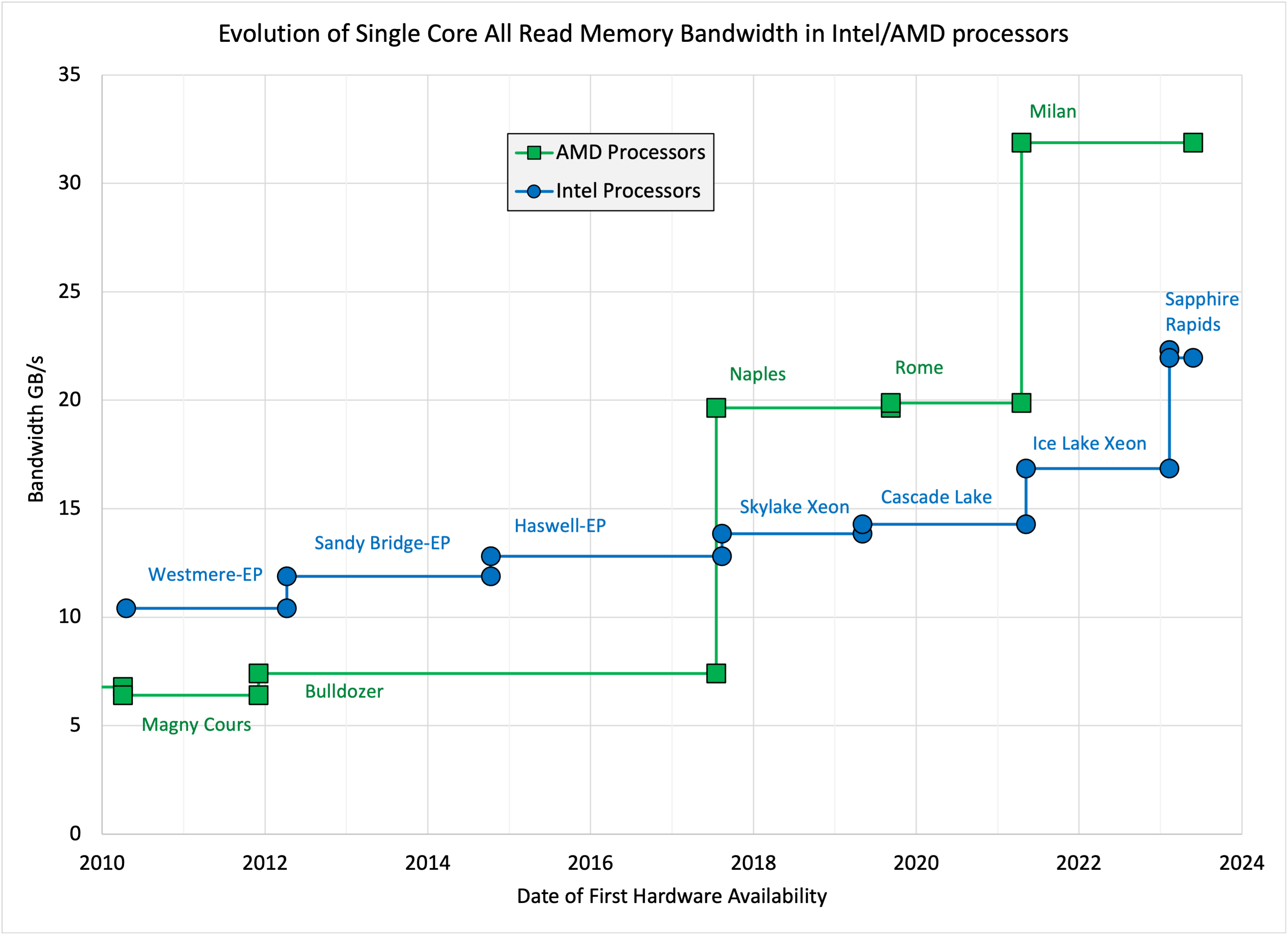
John McCalpin's blog » STREAM benchmark
Cyber Corp Case 2 Writeup - Part 2
Recomendado para você
-
 demonstrate custom exceptions inheritance java - Stack Overflow24 abril 2025
demonstrate custom exceptions inheritance java - Stack Overflow24 abril 2025 -
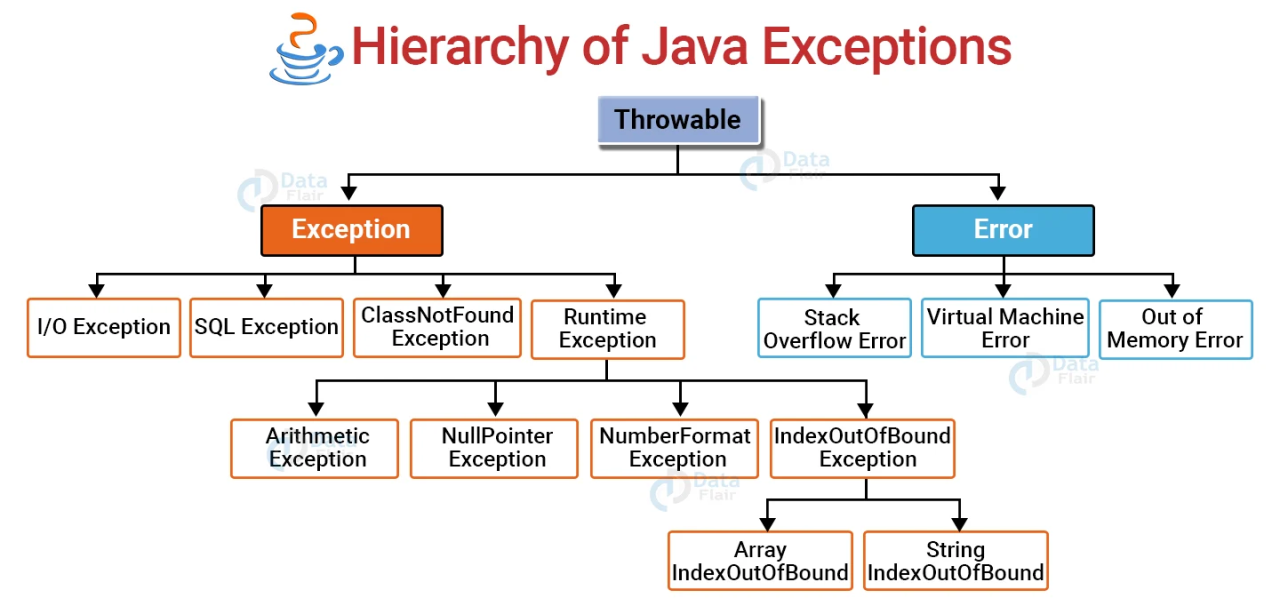
Types of Exceptions in Java24 abril 2025
-
Python Exceptions24 abril 2025
-
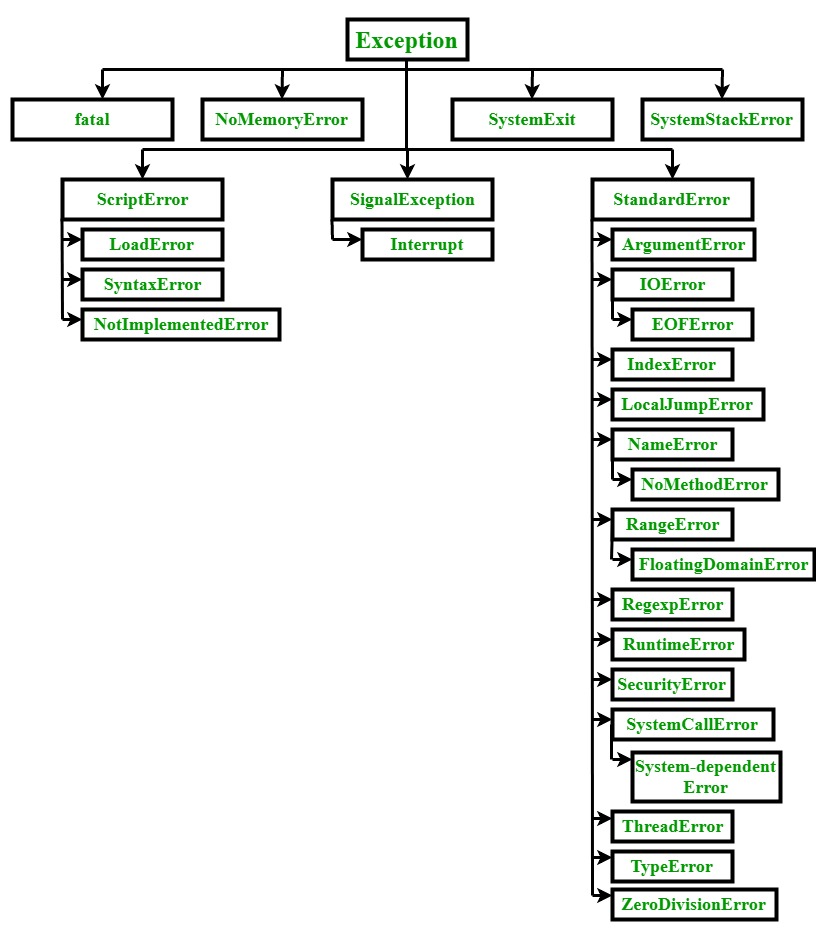 Ruby Exceptions - GeeksforGeeks24 abril 2025
Ruby Exceptions - GeeksforGeeks24 abril 2025 -
 Exceptions and Exception Handling in C#24 abril 2025
Exceptions and Exception Handling in C#24 abril 2025 -
 Exceptions in Java - How to Program with Java24 abril 2025
Exceptions in Java - How to Program with Java24 abril 2025 -
 Best Exception Royalty-Free Images, Stock Photos & Pictures24 abril 2025
Best Exception Royalty-Free Images, Stock Photos & Pictures24 abril 2025 -
🚀Mastering Error and Exception Handling: A Deep Dive into Reliable Code Execution 💻✨24 abril 2025
-
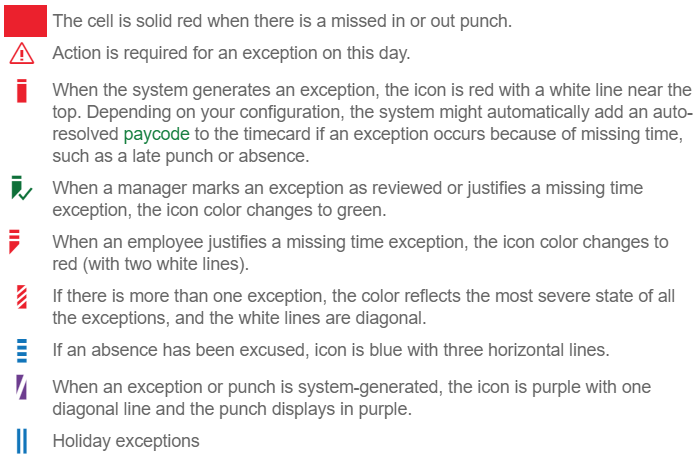 Resolve Timecard Exceptions - Hourly Timecard24 abril 2025
Resolve Timecard Exceptions - Hourly Timecard24 abril 2025 -
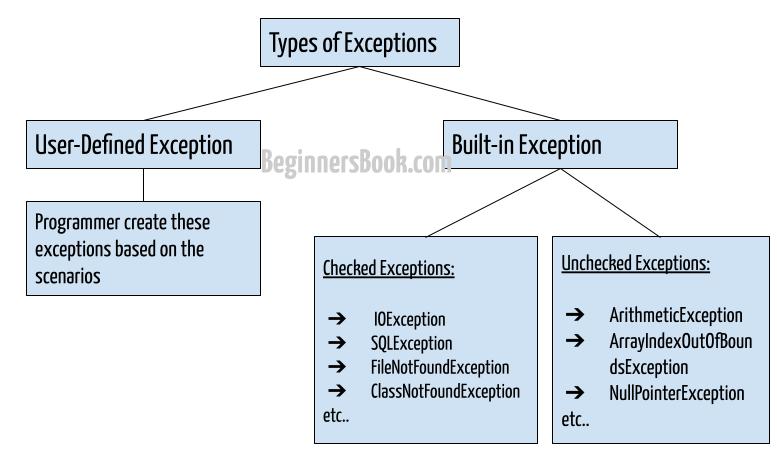 Exception handling in Java with examples24 abril 2025
Exception handling in Java with examples24 abril 2025
você pode gostar
-
 Onde assistir à série de TV Fruits Basket (2019) em streaming on24 abril 2025
Onde assistir à série de TV Fruits Basket (2019) em streaming on24 abril 2025 -
 Roblox Skin Minecraft Skin24 abril 2025
Roblox Skin Minecraft Skin24 abril 2025 -
 Os 10 melhores jogos de 2023 até agora, segundo a crítica24 abril 2025
Os 10 melhores jogos de 2023 até agora, segundo a crítica24 abril 2025 -
 Camisa Titular HNK Rijeka 2023-2424 abril 2025
Camisa Titular HNK Rijeka 2023-2424 abril 2025 -
 The Sims™ Mobile Hack24 abril 2025
The Sims™ Mobile Hack24 abril 2025 -
 Murder Mystery - A Deadly Drama' - Queens Theatre24 abril 2025
Murder Mystery - A Deadly Drama' - Queens Theatre24 abril 2025 -
 Assistir Kamisama Hajimemashita◎ 2° temporada - Episódio 07 Online - Download & Assistir Online! - AnimesTC24 abril 2025
Assistir Kamisama Hajimemashita◎ 2° temporada - Episódio 07 Online - Download & Assistir Online! - AnimesTC24 abril 2025 -
 CRUZEIRO ESPORTE CLUBE (ACRE) em 2023 Cruzeiro esporte clube, Cruzeiro esporte, Cruzeiro24 abril 2025
CRUZEIRO ESPORTE CLUBE (ACRE) em 2023 Cruzeiro esporte clube, Cruzeiro esporte, Cruzeiro24 abril 2025 -
![UPD 17.3] MELHORES FRUTAS PARA PVP E BOUNTY HUNTER DO BLOX FRUITS](https://i.ytimg.com/vi/aLuUjH_L-ZE/maxresdefault.jpg) UPD 17.3] MELHORES FRUTAS PARA PVP E BOUNTY HUNTER DO BLOX FRUITS24 abril 2025
UPD 17.3] MELHORES FRUTAS PARA PVP E BOUNTY HUNTER DO BLOX FRUITS24 abril 2025 -
![Dead Space Review [PS5] A Remake Done Right - GameByte](https://www.gamebyte.com/wp-content/uploads/2021/08/abcbf308-featured-images-for-website-94-scaled.jpg) Dead Space Review [PS5] A Remake Done Right - GameByte24 abril 2025
Dead Space Review [PS5] A Remake Done Right - GameByte24 abril 2025