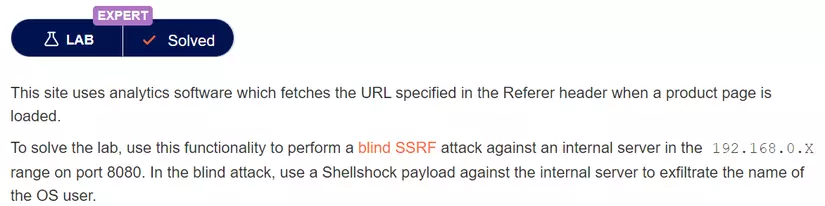
Lab: Blind SSRF with Shellshock exploitation
Por um escritor misterioso
Last updated 25 abril 2025

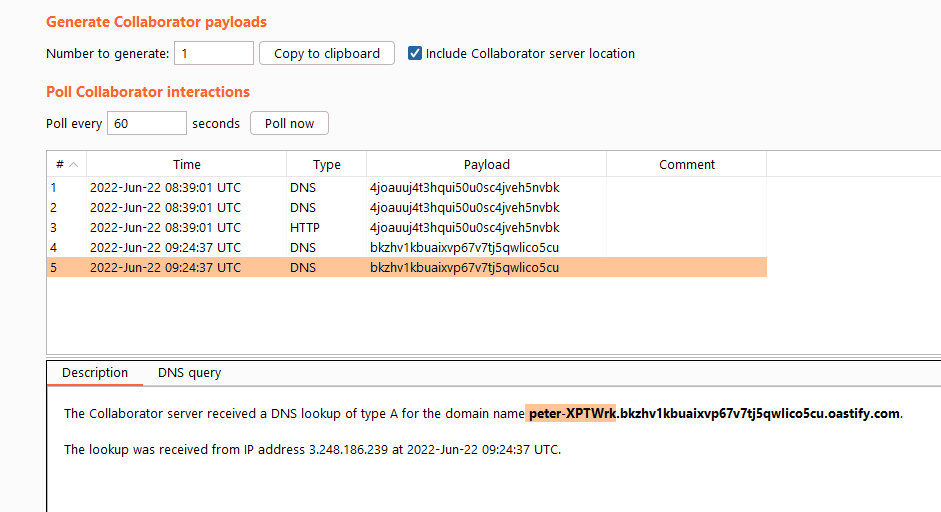
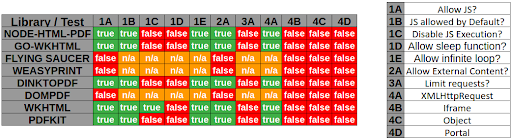
This site uses analytics software which fetches the URL specified in the Referer header when a product page is loaded. To solve the lab, use this
Web Security Academy Series Course

HackMD - Collaborative Markdown Knowledge Base
Web Application Hacking - Server-Side Request Forgery
PayloadsAllTheThings/Server Side Request Forgery/README.md at

PortSwigger SSRF Labs. Hey all! This write-up is about my…
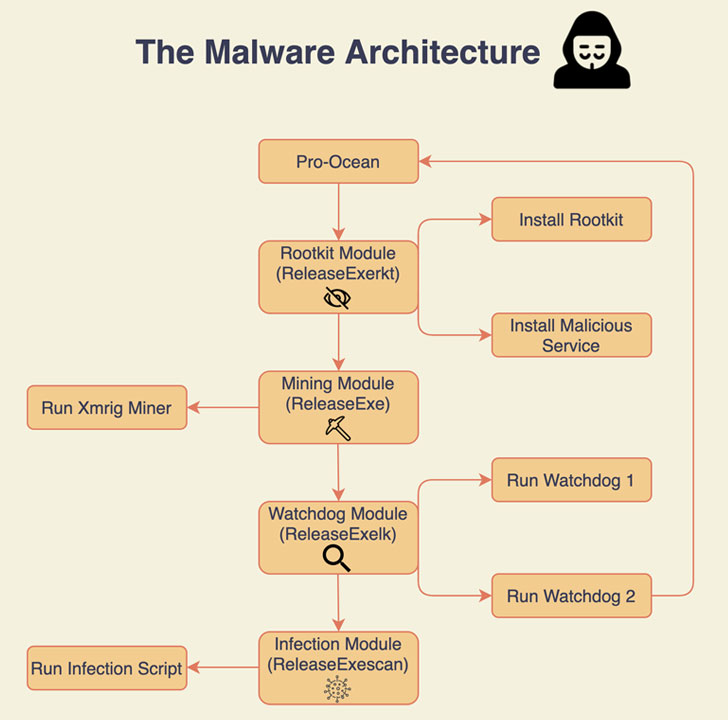
New Cryptojacking Malware Targeting Apache, Oracle, Redis Se

Blind SSRF exploitation ❗️ - Wallarm

Blind SSRF with Shellshock exploitation (Video solution)

SSRF(服务器跨站请求伪造)基础知识- lca
Solving PortSwigger SSRF Labs - Final Part - ::: re:search + re
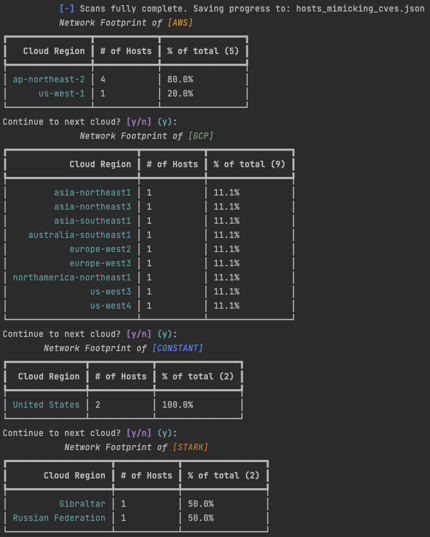
An Attacker's Guide to Evading Honeypots - Part 3
Server side request forgery vulnerabilities (SSRF) - Các lỗ hổng
Recomendado para você
-
 Hack the… Pulley - LEGO® Technic™ Videos - for kids25 abril 2025
Hack the… Pulley - LEGO® Technic™ Videos - for kids25 abril 2025 -
 Yahoo hack wasn't Shellshock, company claims, The Independent25 abril 2025
Yahoo hack wasn't Shellshock, company claims, The Independent25 abril 2025 -
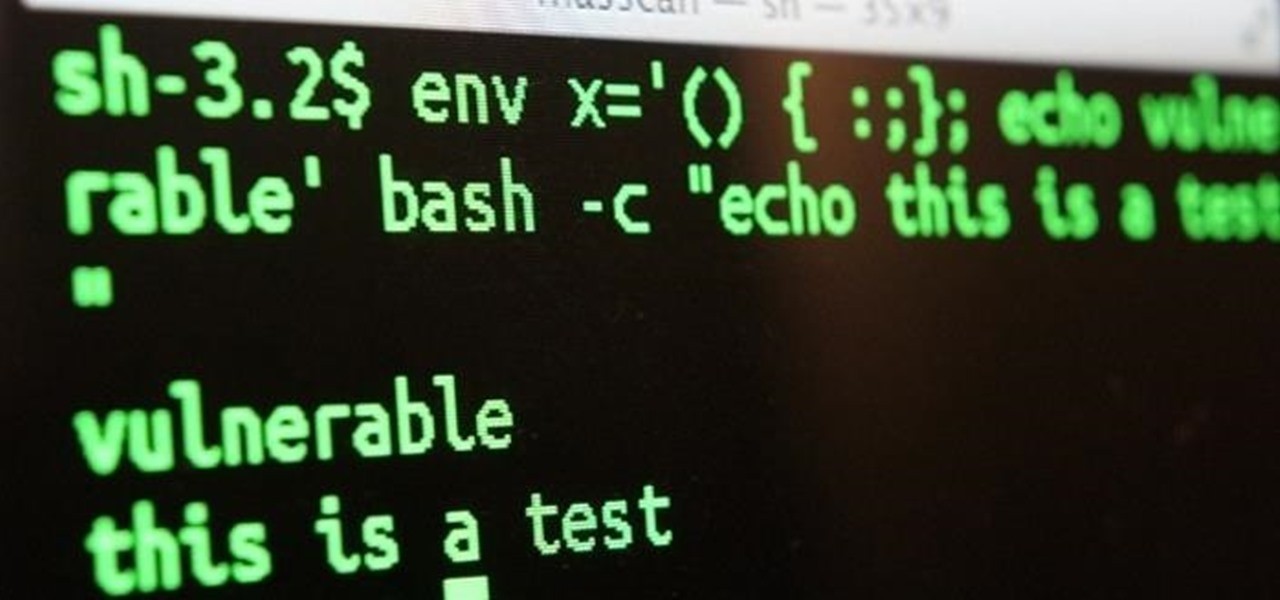
ShellShock Vulnerability25 abril 2025
-
 Shellshock – Find out if your mobile device is vulnerable - Zimperium25 abril 2025
Shellshock – Find out if your mobile device is vulnerable - Zimperium25 abril 2025 -
Shellshock: Bash software bug leaves up to 500 million computers at risk of hacking - ABC News25 abril 2025
-
 Shellshock Security Flaw - What is it and how it affects everyone - My Blog25 abril 2025
Shellshock Security Flaw - What is it and how it affects everyone - My Blog25 abril 2025 -
 Shellshock proves open source's 'many eyes' can't see straight25 abril 2025
Shellshock proves open source's 'many eyes' can't see straight25 abril 2025 -
 Hacks - TMNT of Rage - The Final Shell Shock & Re-Shelled25 abril 2025
Hacks - TMNT of Rage - The Final Shell Shock & Re-Shelled25 abril 2025 -
 Are you suffering from ShellShock? - Infosec Partners25 abril 2025
Are you suffering from ShellShock? - Infosec Partners25 abril 2025 -
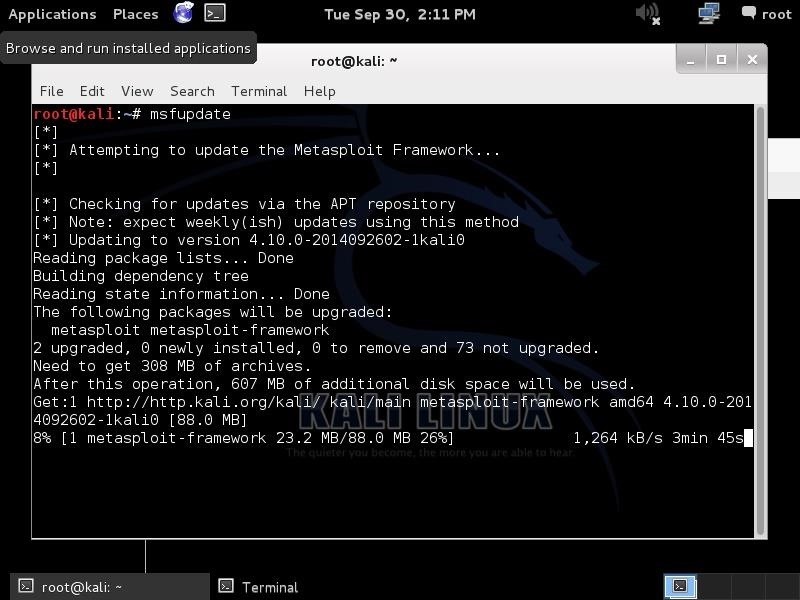 Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null25 abril 2025
Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null25 abril 2025
você pode gostar
-
 Boys Basketball: Trinity wins on buzzer beater, Cumberland Valley, Shippensburg, Cedar Cliff extend winning streaks and other notes from Tuesday's games25 abril 2025
Boys Basketball: Trinity wins on buzzer beater, Cumberland Valley, Shippensburg, Cedar Cliff extend winning streaks and other notes from Tuesday's games25 abril 2025 -
 Uber Shot On Iphone GIF - Uber Shot On Iphone Tommy S - Discover & Share GIFs25 abril 2025
Uber Shot On Iphone GIF - Uber Shot On Iphone Tommy S - Discover & Share GIFs25 abril 2025 -
![SFM/FNAF/SB/OC] - Big Sister Roxy by WildCatStudios898 on DeviantArt](https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/77672deb-12c0-49c6-9169-7463fa6688f9/df098yc-e0683125-8c18-4002-9d92-8590886247c6.png/v1/fill/w_1192,h_670,q_70,strp/_sfm_fnaf_sb_oc____big_sister_roxy_by_wildcatstudios898_df098yc-pre.jpg?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOjdlMGQxODg5ODIyNjQzNzNhNWYwZDQxNWVhMGQyNmUwIiwiaXNzIjoidXJuOmFwcDo3ZTBkMTg4OTgyMjY0MzczYTVmMGQ0MTVlYTBkMjZlMCIsIm9iaiI6W1t7ImhlaWdodCI6Ijw9MTA4MCIsInBhdGgiOiJcL2ZcLzc3NjcyZGViLTEyYzAtNDljNi05MTY5LTc0NjNmYTY2ODhmOVwvZGYwOTh5Yy1lMDY4MzEyNS04YzE4LTQwMDItOWQ5Mi04NTkwODg2MjQ3YzYucG5nIiwid2lkdGgiOiI8PTE5MjAifV1dLCJhdWQiOlsidXJuOnNlcnZpY2U6aW1hZ2Uub3BlcmF0aW9ucyJdfQ.DIyhOtu1ayVaLqHauGWbGQLUIUPBdeJbQntpBgbLhrw) SFM/FNAF/SB/OC] - Big Sister Roxy by WildCatStudios898 on DeviantArt25 abril 2025
SFM/FNAF/SB/OC] - Big Sister Roxy by WildCatStudios898 on DeviantArt25 abril 2025 -
A co-op cooking game where you can only use one arm to cook, check25 abril 2025
-
 Análise: Mortal Kombat 11 Ultimate (Multi) é a versão definitiva25 abril 2025
Análise: Mortal Kombat 11 Ultimate (Multi) é a versão definitiva25 abril 2025 -
 Rian Johnson Frustrated by Star Wars Fans' Misconceptions of Last25 abril 2025
Rian Johnson Frustrated by Star Wars Fans' Misconceptions of Last25 abril 2025 -
 GUIA SUPREMO dos Melhores Jogos do Nintendo Switch Atualizado 202325 abril 2025
GUIA SUPREMO dos Melhores Jogos do Nintendo Switch Atualizado 202325 abril 2025 -
 Whale Sharks in Video Games, Where to Swim with the Gentle Giants25 abril 2025
Whale Sharks in Video Games, Where to Swim with the Gentle Giants25 abril 2025 -
 Round 6: seis coisas que a série da Netflix nos ensina sobre a realidade da Coreia do Sul - BBC News Brasil25 abril 2025
Round 6: seis coisas que a série da Netflix nos ensina sobre a realidade da Coreia do Sul - BBC News Brasil25 abril 2025 -
 File:Esteghlal FC vs Sanat Naft Abadan FC, 5 November 2019 - 137.jpg - Wikipedia25 abril 2025
File:Esteghlal FC vs Sanat Naft Abadan FC, 5 November 2019 - 137.jpg - Wikipedia25 abril 2025