PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 11 abril 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
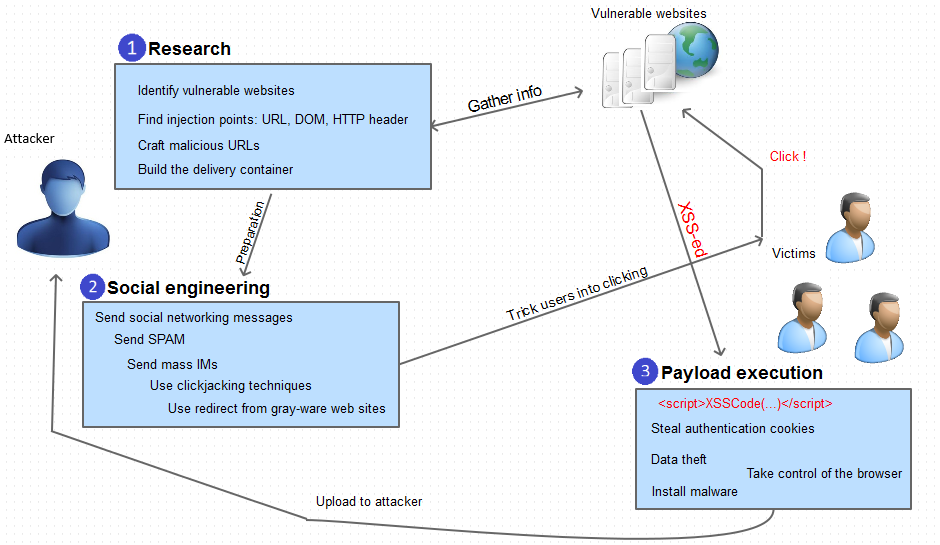
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.inspectiv.com/hubfs/Inspectiv_December2022/images/61cccea250b8fe03e2c3aec2_Screen-Shot-2021-05-19-at-7.52.57-AM.png)
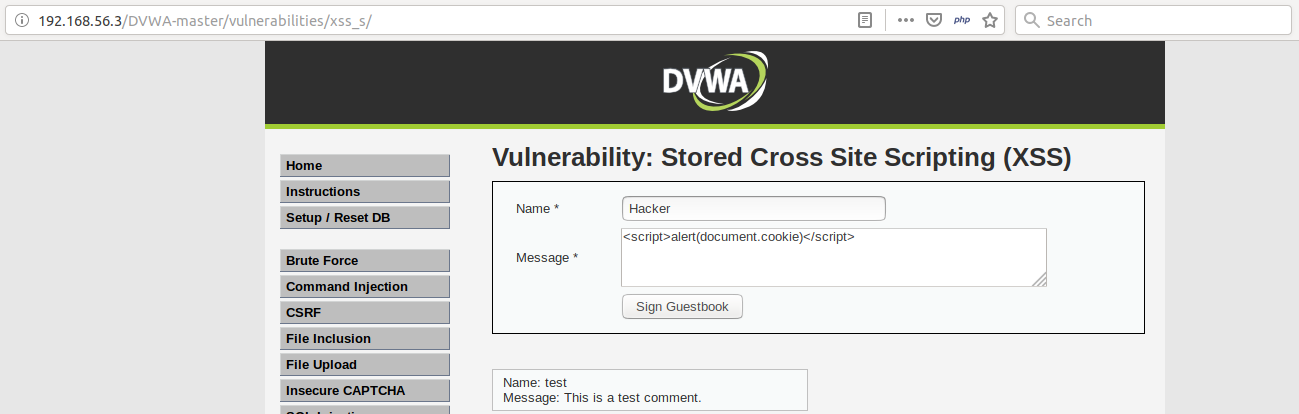
Differences of Stored XSS and Reflected XSS
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Table1-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://i1.rgstatic.net/publication/346647963_A_Tutorial_on_Cross_Site_Scripting_Attack_-_Defense/links/5fcb62c8299bf188d4f605f2/largepreview.png)
PDF) A Tutorial on Cross Site Scripting Attack - Defense
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://dfzljdn9uc3pi.cloudfront.net/2017/cs-136/1/fig-1-2x.jpg)
Fatal injection: a survey of modern code injection attack countermeasures [PeerJ]
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://ietresearch.onlinelibrary.wiley.com/cms/asset/a9b8a20f-14af-4dcc-ab69-583b7ea5ad73/cps212047-toc-0001-m.jpg?trick=1700749027190)
Inferring adversarial behaviour in cyber‐physical power systems using a Bayesian attack graph approach - Sahu - 2023 - IET Cyber-Physical Systems: Theory & Applications - Wiley Online Library
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs13174-019-0115-x/MediaObjects/13174_2019_115_Fig1_HTML.png)
Detecting web attacks with end-to-end deep learning, Journal of Internet Services and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://cdn.acunetix.com/wp_content/uploads/2010/09/sql_inj_xss.gif)
SQL Injection - MDN Web Docs Glossary: Definitions of Web-related terms
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Figure4-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Anny-Leema/publication/329683964/figure/fig4/AS:932153105846273@1599254027775/Analysis-of-various-services-in-Anti-XSS_Q320.jpg)
PDF) Eradicating cross site scripting attack for a secure web access
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1007%2Fs11036-022-02052-z/MediaObjects/11036_2022_2052_Fig3_HTML.png)
Defining Cross-Site Scripting Attack Resilience Guidelines Based on BeEF Framework Simulation
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://images.ctfassets.net/4un77bcsnjzw/1ABjVui53sICnyiBxPduPO/6efb664e2b908f2f394abc8ca755dd6a/XSS_Mitigation.svg)
What is cross-site scripting (XSS)?, Tutorial & examples
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs40537-022-00678-0/MediaObjects/40537_2022_678_Fig1_HTML.png)
Detection and prevention of SQLI attacks and developing compressive framework using machine learning and hybrid techniques, Journal of Big Data
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Leandros-Maglaras/publication/346647963/figure/fig5/AS:965332541902851@1607164621685/Webpage-after-mitigation_Q320.jpg)
PDF) A Tutorial on Cross Site Scripting Attack - Defense
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs13174-019-0115-x/MediaObjects/13174_2019_115_Fig7_HTML.png)
Detecting web attacks with end-to-end deep learning, Journal of Internet Services and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-security/sase-sse-ag.docx/_jcr_content/renditions/sase-sse-ag_0.jpg)
Solutions - Cisco Secure Access Service Edge (SASE) and Security Service Edge (SSE) Architecture Guide - Cisco
Recomendado para você
-
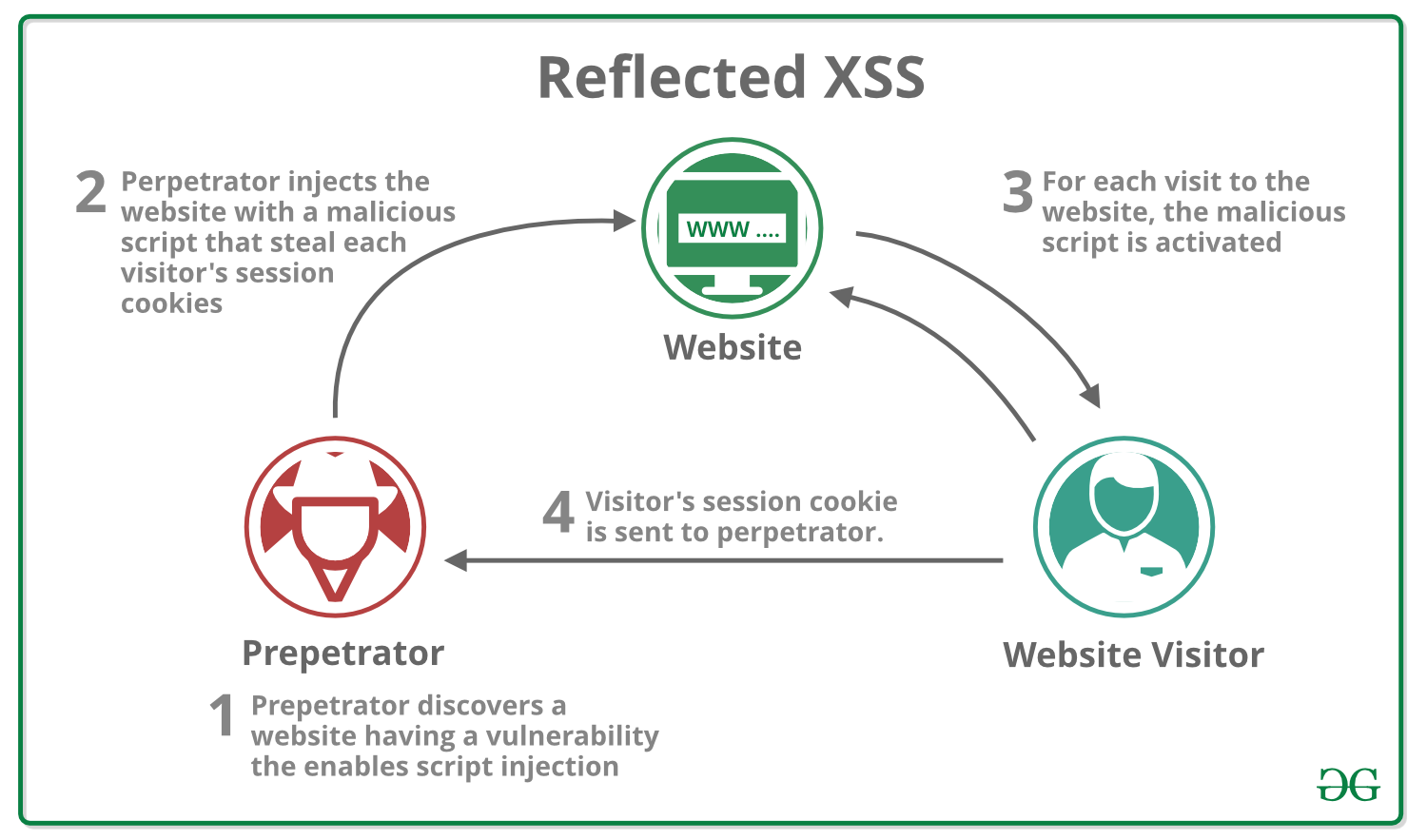 What is Cross Site Scripting (XSS) ? - GeeksforGeeks11 abril 2025
What is Cross Site Scripting (XSS) ? - GeeksforGeeks11 abril 2025 -
5: Cross-site scripting (XSS) attack (Source Coursera) [8011 abril 2025
-
 SQL injection and cross-site scripting: The differences and attack11 abril 2025
SQL injection and cross-site scripting: The differences and attack11 abril 2025 -
 How To Protect Your Website Against A Cross-Site Scripting (XSS11 abril 2025
How To Protect Your Website Against A Cross-Site Scripting (XSS11 abril 2025 -
 Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS11 abril 2025
Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS11 abril 2025 -
 What is Cross-Site Scripting? XSS Cheat Sheet11 abril 2025
What is Cross-Site Scripting? XSS Cheat Sheet11 abril 2025 -
 What Is Cross Site Scripting and How to Avoid XSS Attacks?11 abril 2025
What Is Cross Site Scripting and How to Avoid XSS Attacks?11 abril 2025 -
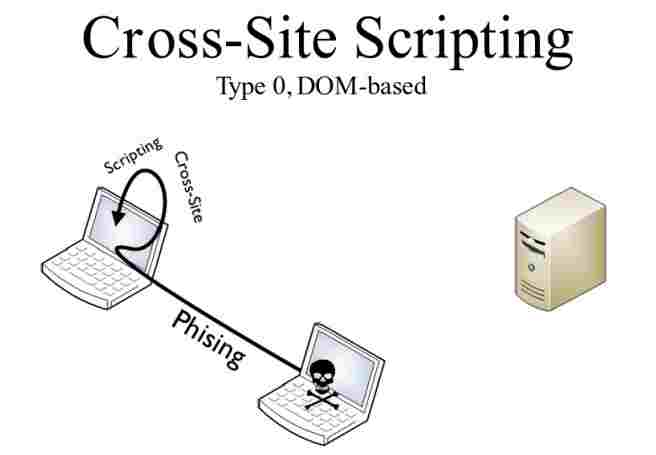 DOM Based XSS Attack Tutorial - How it works?11 abril 2025
DOM Based XSS Attack Tutorial - How it works?11 abril 2025 -
 Vulnérabilité XSS, ou injection de code indirecte à distance11 abril 2025
Vulnérabilité XSS, ou injection de code indirecte à distance11 abril 2025 -
What Is Cross Site Scripting and How to Prevent It? A Complete11 abril 2025
você pode gostar
-
 Cosmic Fear Mode Garou (One Punch Man) VS RWBY Gods (RWBY) SPOILERS!, Page 211 abril 2025
Cosmic Fear Mode Garou (One Punch Man) VS RWBY Gods (RWBY) SPOILERS!, Page 211 abril 2025 -
 Estrela Vermelha x Partizan Belgrado, um dos maiores clássicos do mundo11 abril 2025
Estrela Vermelha x Partizan Belgrado, um dos maiores clássicos do mundo11 abril 2025 -
 Xiaomi Mi Box 4k Android Tv Media Player Hdr Xiaomi Mi Box 4k Android Tv 9.0 - Box - Aliexpress11 abril 2025
Xiaomi Mi Box 4k Android Tv Media Player Hdr Xiaomi Mi Box 4k Android Tv 9.0 - Box - Aliexpress11 abril 2025 -
 2 carteles de bienvenida en español, carteles inspiradores, carteles motivacionales españoles con 40 puntos adhesivos para niños pequeños11 abril 2025
2 carteles de bienvenida en español, carteles inspiradores, carteles motivacionales españoles con 40 puntos adhesivos para niños pequeños11 abril 2025 -
 Gaudium Events International School In Hyderabad11 abril 2025
Gaudium Events International School In Hyderabad11 abril 2025 -
 PlayStation VR2 review11 abril 2025
PlayStation VR2 review11 abril 2025 -
 Motors - APK Download for Android11 abril 2025
Motors - APK Download for Android11 abril 2025 -
 Pac-Man 99 Review - Pac-Man 99 Review – A Great Game To Play While Doing Something Else - Game Informer11 abril 2025
Pac-Man 99 Review - Pac-Man 99 Review – A Great Game To Play While Doing Something Else - Game Informer11 abril 2025 -
dragonblade riven11 abril 2025
-
 Various shallots. Let's see if reddit let's me keep all 3 images or edits it down again :// : r/DragonballLegends11 abril 2025
Various shallots. Let's see if reddit let's me keep all 3 images or edits it down again :// : r/DragonballLegends11 abril 2025